In crypto, a wallet isn’t a pocket for coins-it’s a set of keys to a vault you can’t see. How you hold those keys shapes everything from your day‑to‑day convenience to your exposure to risk. That’s where the long-running debate begins: hardware wallets-the dedicated devices built to keep keys offline-and software wallets-the apps that live on your phone or laptop and meet you where you trade, pay, and explore.
The story isn’t as simple as “cold is safe, hot is easy.” Both camps have strengths, blind spots, and myths that refuse to die. Hardware adds physical separation but introduces its own concerns: cost, handling, supply chain trust, and the human factor of backups. Software shines in speed and access but sits closer to malware, phishing, and the friction of staying secure while staying connected.
This article compares hardware and software wallets through the lenses that actually matter: security models and threat surfaces, usability and mobility, cost and maintenance, recovery and resilience, privacy, compatibility with DeFi and NFTs, and the realities of travel and regulation. We’ll outline typical user profiles-from long‑term holders to daily power users-and map them to practical setups, including hybrid approaches like pairing a hardware signer with a software interface or using multisig.
By the end, you won’t get a one‑size‑fits‑all verdict. You’ll get a clear frame for choosing the right tool-or combination-for your assets, habits, and risk tolerance.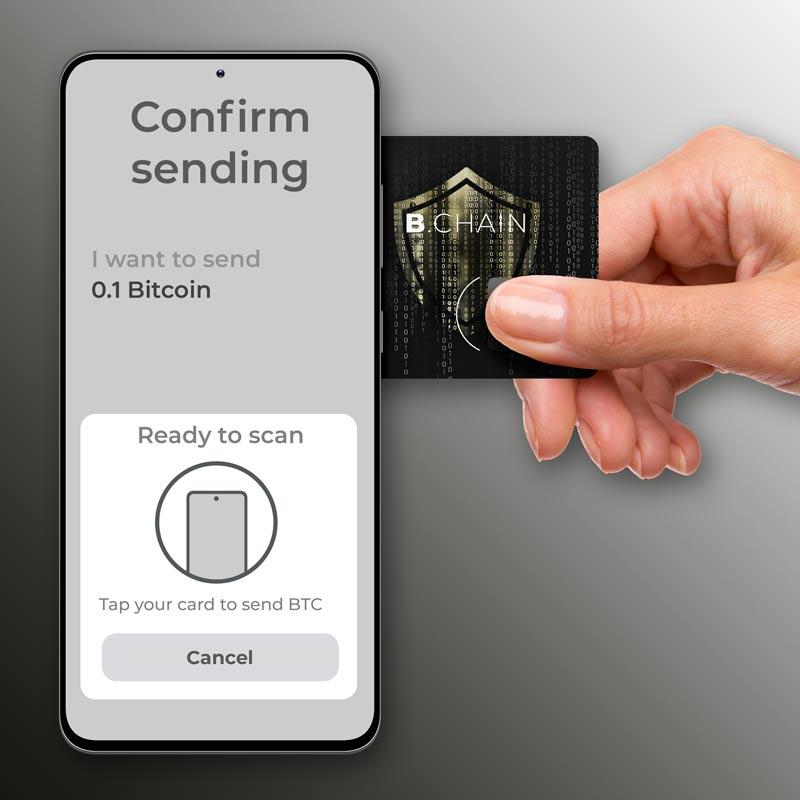
Security under real world threats and when cold storage truly helps
Out in the wild, attackers go for whatever’s easiest: your browser extensions, mobile OS, auto-approved dApps, and sloppy seed handling. Software wallets excel at speed and convenience, but their permanent network exposure widens the blast radius. Hardware wallets reduce that surface by isolating keys and forcing on-device review. The real question isn’t “which is safer,” it’s “safer against what.” Remote malware, clipboard hijackers, and deceptive signing prompts are blunted by an offline signer; targeted physical theft, coercion, or tampered shipments demand different defenses and procedures.
- Phishing & blind signing: Verify human-readable details on-device; avoid blind signing; use allowlists.
- Clipboard/address swap malware: Trust the address on your device screen, not your computer.
- SIM-swap & cloud backups: Don’t store seeds in the cloud; add a passphrase and hardware-gated restores.
- OS compromise (RATs/keyloggers): Prefer PSBTs via QR/microSD; keep keys air‑gapped.
- Physical theft/loss: Enforce PIN delays, auto-wipe, and passphrase-protected vaults.
- Coercion/travel risk: Use duress PINs, plausible-deniability accounts, and multisig split across locations.
| Threat | Vulnerable Surface | Hardware Edge | Cold Storage Move |
|---|---|---|---|
| Phishing dApp | Hot browser wallet | On-device decoding | PSBT/QR only; reject unknown domains |
| Clipboard swap | Desktop wallet | Address shown on device | Confirm outputs; test sends |
| SIM swap + cloud | Mobile restore | Seed never on phone | Disable cloud; add passphrase |
| RAT/keylogger | Laptop OS | Isolated signer | Air-gapped PSBT via microSD |
| Home burglary | Any single device | PIN + wipe | 2-of-3 multisig, geo-split |
| Coercion | User under duress | Duress wallet | Small decoy + time delays |
| Supply-chain | New device | Secure boot/attest | Buy direct; verify firmware |
Cold storage shines when your priority is time, distance, and friction: long-term holdings, infrequent moves, and high assurance that a remote adversary can’t transact even if they control your computer. Pair a hardware signer with clear rules-spending caps, multi-person approvals, and multisig across locations-to separate what you use daily from what must never touch the internet. A practical pattern is to keep “vault” funds offline, “warm” capital in a limited multisig for periodic rebalancing, and “hot” funds small for day‑to‑day use. Test restores, rotate backups, and document recovery so security isn’t lost to forgetfulness.

Everyday use setup seed security backups and recovery without friction
Everyday usability rests on two pillars: speed and certainty. Mobile apps launch fast, auto-detect networks, and pair with dApps in a tap-great for coffee-line payments and micro-swaps. Dedicated devices counter with offline key creation, on-screen verification, and physical buttons that prevent “fat-finger” approvals. For keys, apps often nudge you toward encrypted backups and biometrics, while devices guide you through writing the seed safely without exposing it to the internet. The smoothest routines blend both: a phone wallet for low-stakes activity, paired to a hardware signer for approvals above a set limit.
- Hardware wins at final checks: clear signing, NFC/QR workflows, auto-lock, and optional passphrases for vaults.
- Software wins at convenience: biometric unlock, fast network switching, WalletConnect, and encrypted cloud snapshots (when properly set up).
- Hybrid flow: everyday taps on phone, large moves confirmed on-device, with alerts for transactions above your threshold.
Backups and recovery should feel uneventful-and verifiable. A 12/24‑word phrase is still the common denominator; devices encourage metal backups or Shamir splits for redundancy, while apps offer local encrypted exports and optional cloud key vaults. Add a passphrase for deniability, label your recovery kits, and schedule a five-minute test-restore on day one. Keep a simple runbook: where the seed lives, who can access it, and how to re-derive accounts. When a phone or device fails, the goal is minutes-not hours-to be transacting again.
| Action | Hardware Wallet | Software Wallet |
|---|---|---|
| New device setup | Offline seed; guided steps | Fast install; app wizard |
| Seed backup | Paper/metal; Shamir optional | Encrypted file/cloud; passphrase |
| Recovery time | Moderate; plug and restore | Quick; restore and sync |
| Loss/theft impact | Low if PIN/passphrase set | Low if device lock + backup |

Total cost of ownership support lifespan and when a hardware wallet pays off
Look beyond sticker price and think in terms of the whole journey. A dedicated device has an upfront hit, but its value is tied to how long the vendor ships updates, how often you transact, and what level of resilience you want. Support windows matter: some brands maintain firmware for years and their secure element or OS continues to receive patches, while a phone-based app rides on the phone’s own update cycle. Factor in replacement plans (lost, damaged, or upgraded devices), the cost of secure backups (steel plates or duplicating keys), and the time you’ll spend on recovery drills to keep redundancy real.
- Upfront: device price, shipping, optional metal backup.
- Maintenance: firmware updates, cables/dongles, optional premium services.
- Lifecycle: vendor support horizon, OS compatibility, eventual upgrades.
- Risk-adjusted cost: time to verify addresses, confirm prompts, run test restores.
- Opportunity: safer dApp signing, travel peace-of-mind, multisig cosigning.
When does a device financially make sense? A pragmatic rule is to amortize the purchase over 3-5 years and weigh it against what you’re protecting and how you use it. If you’d comfortably spend 1-2% of your holdings to reduce malware and phishing exposure, a device starts to make sense around the mid four figures-earlier if you’re active with DeFi approvals or you travel. For smaller, short-term balances, a well-hardened mobile or desktop app-kept on a clean OS with biometric/OS-level isolation-can be perfectly rational. For long horizons, larger portfolios, shared custody, or frequent on-chain interactions, hardware (often as a multisig cosigner) tends to pay for itself through fewer close calls and clearer transaction prompts.
| Portfolio | Horizon | Payoff Likelihood | Notes |
|---|---|---|---|
| < $1k | < 1 year | Low | Hardened software wallet; keep costs minimal. |
| $1k-$10k | 1-3 years | Medium | Pays off with dApps, travel, or frequent signing. |
| $10k-$50k | 3+ years | High | Hardware + passphrase or 2-of-3 multisig. |
| > $50k | 3+ years | Very High | Dual-vendor setup; documented recovery tests. |

Recommendations by portfolio size trading frequency and travel needs
Match your setup to your balance and pace. For small stacks and occasional buys, convenience wins; as holdings grow or you click “confirm” more often, lean on dedicated signers and clear separation between cold storage and hot spending. Use watch‑only views to track without exposing keys, and keep recovery hygiene tight with off‑device backups.
- Under $1k, rare trades: Mobile software wallet with biometric lock; manual on‑ramp; zero custodial storage.
- $1k-$50k, weekly/monthly: Hardware signer + mobile wallet (watch‑only); withdraw to self‑custody after each session; enable passphrase.
- Over $50k, low frequency: Multi‑sig with 2-3 hardware devices; offline PSBT signing; steel backup split across locations.
- High‑frequency traders: Keep a small hot float; automate exchange withdrawals to allowlisted addresses; park the bulk on a hardware or multi‑sig vault.
- NFT/gaming: Use a separate “burner” wallet for mints; sign expensive transfers with hardware only.
Mobility changes your threat model. If you travel often, minimize what you carry, cap hot balances, and prepare for device loss or inspection. Keep your deep storage stationary, sign offline when feasible, and use duress features sparingly and legally.
| Profile | Primary Setup | Hot Float | Extras |
| Desk Investor | Hardware + desktop | $0-$100 | Price alerts only |
| Mobile Swing | Mobile + hardware signer | $500-$2k | 2FA + allowlist |
| Frequent Flyer | Travel hot; vault at home | $200-$800 | Duress PIN; remote wipe |
| Long‑Term Whale | 2‑of‑3 multi‑sig | $0 | Offline PSBT only |
In Conclusion
In the end, choosing between a hardware wallet and a software wallet isn’t a verdict-it’s a fit check. Security and convenience sit on a sliding scale, and where you land depends on how often you transact, what you hold, and what you’re protecting against. Hardware can feel like a vault for long-term peace of mind; software can feel like a well-lit dashboard for everyday use. Many people end up with both: a cold place to park value and a warm place to move it.
Whichever route you take, the fundamentals don’t change: safeguard your recovery phrase, test restores before you need them, keep firmware and apps updated, and be wary of phishing and supply-chain tricks. The landscape is shifting, too-multi-party computation, secure enclaves, and account abstraction are narrowing old gaps-so revisit your setup as your needs and the tools evolve.
Think of your wallet not just as a device or an app, but as a habit. Pick the gear that matches your journey, build simple routines around it, and let your process-not panic-do the heavy lifting.
