On a quiet ward, the most valuable resource is trust: that a medication is genuine, that a record is complete, that consent is current, that every handoff leaves a trace. Healthcare has digitized much of its workflow, yet the seams still show-systems don’t always agree, provenance is hard to prove, and coordination across institutions is often fragile. Into this gap steps an unlikely tool from the world of distributed systems: blockchains and related ledger technologies.
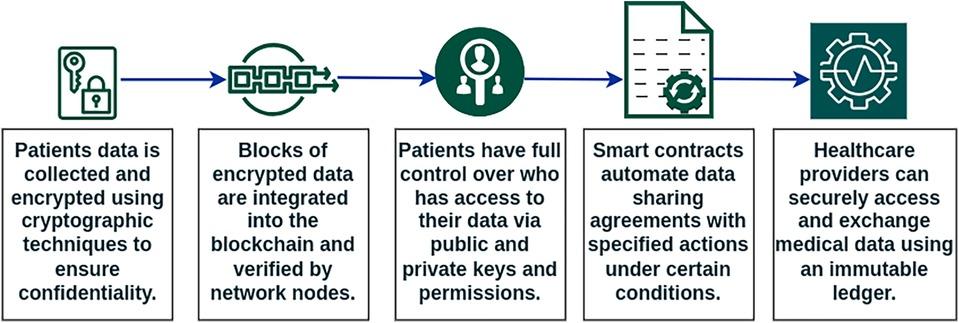
This isn’t about coins at the bedside. It’s about shared, tamper-evident logs, programmable rules, and verifiable credentials that multiple organizations can rely on without surrendering control. In healthcare, that can mean tracing a drug’s journey to the infusion pump, making patient consent portable and auditable, validating a clinician’s credentials in minutes rather than months, or anchoring clinical trial data so deviations can’t be quietly rewritten. It can also support privacy-preserving data sharing-proving eligibility or authorizing access without placing sensitive information on a public stage.
The promise is real, but so are the constraints. Most clinically sound designs keep protected health information off-chain, use permissioned networks, and lean on standards like FHIR. They demand careful governance, interoperability with existing systems, and clarity about liability, regulation, and human workflows. Energy use, scalability, and latency have improved with modern architectures, yet they still shape what is practical at the point of care.
This article surveys concrete healthcare use cases for blockchains-from supply chain assurance to claims automation, from device data provenance to research registries-and examines how they work, where they fit, and what it takes to move from pilot to practice. The lens is the bedside: not as a boundary, but as the place where technical choices either help clinicians and patients-or get in their way.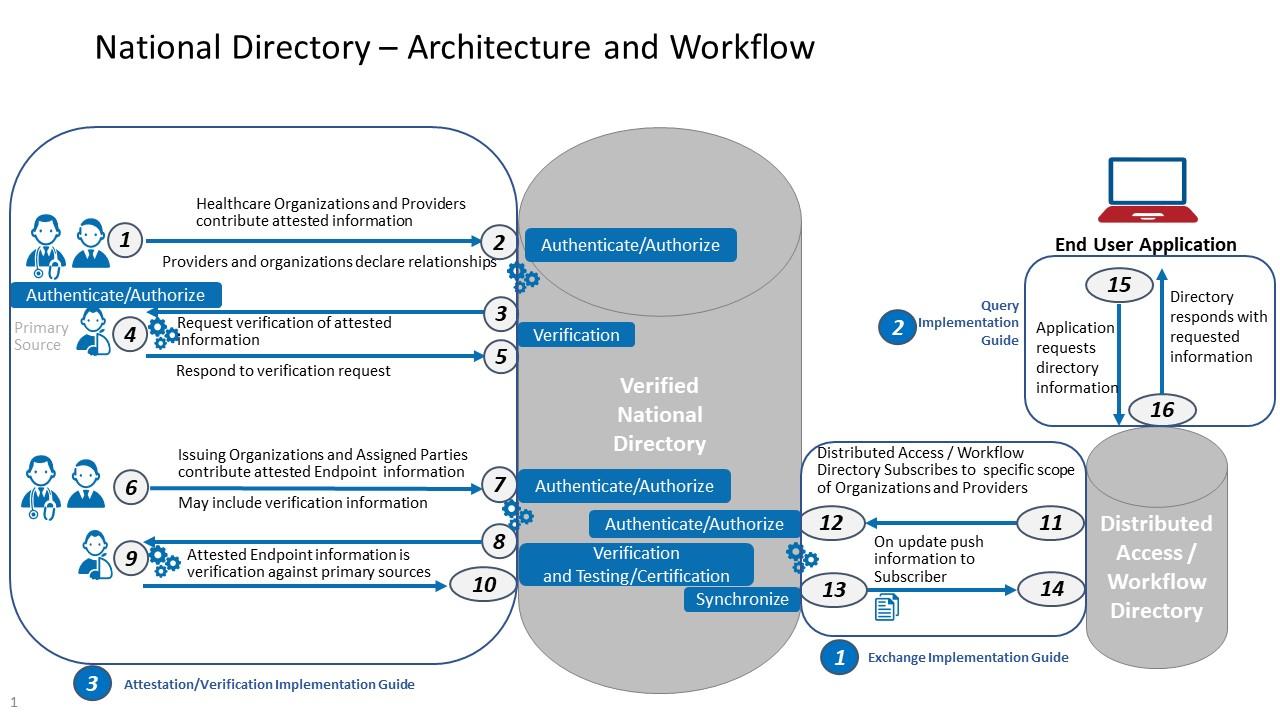
Patient data interoperability and consent orchestration with FHIR verifiable credentials and off chain storage
Imagine bedside data exchange as a cryptographic handshake: a person holds a wallet with FHIR-based verifiable credentials (e.g., MedicationStatement, Consent, Composition) bound to a decentralized identifier (DID), while hospitals and apps verify rights and purpose without pulling raw charts across networks. Consent becomes a tamper-evident receipt anchored on-chain, pointing to encrypted, off‑chain bundles (cloud vaults, data trusts, or IPFS gateways) via content addresses. The chain records proofs and policies; the payload lives elsewhere, reducing risk and vendor lock‑in. Result: fine‑grained access, traceable provenance, and interoperable movement of data across EHRs, HIEs, and research networks-without surrendering control or duplicating sensitive datasets.
Operationally, orchestration centers on capabilities rather than integrations, letting participants prove minimal facts and retrieve only what’s necessary under least privilege and purpose limitation.
- Issue: A clinic issues a FHIR VC (e.g., Immunization) to the patient’s wallet after identity proofing and hashing the source record.
- Request: A researcher or app sends a consent‑aware query describing purpose, FHIR scopes, and data minimization rules.
- Present: The patient selectively discloses claims (e.g., dates, codes) and a signed consent credential; no bulk data moves yet.
- Verify: The requester checks signatures, revocation status, and on‑chain policy references; access is approved per granular scopes.
- Retrieve: Authorized parties fetch encrypted bundles from off‑chain storage using short‑lived tokens; audit hashes land on-chain.
- Revoke/Audit: Consent can be revoked or time‑boxed; every read leaves a verifiable, privacy‑preserving trail.
| Role | Credential (FHIR) | Off‑chain store | On‑chain proof |
|---|---|---|---|
| Patient | Consent, Composition | Encrypted wallet vault | DID, consent receipt hash |
| Provider | Observation, Medication | Clinic data lake | Issuer registry, revocation list |
| Researcher | De‑identified Bundle | Data trust | Purpose tag, query proof |
| Payer | Claim, Coverage | Private cloud | Access attestation |
End to end drug supply assurance with serialization IoT oracles and permissioned ledgers
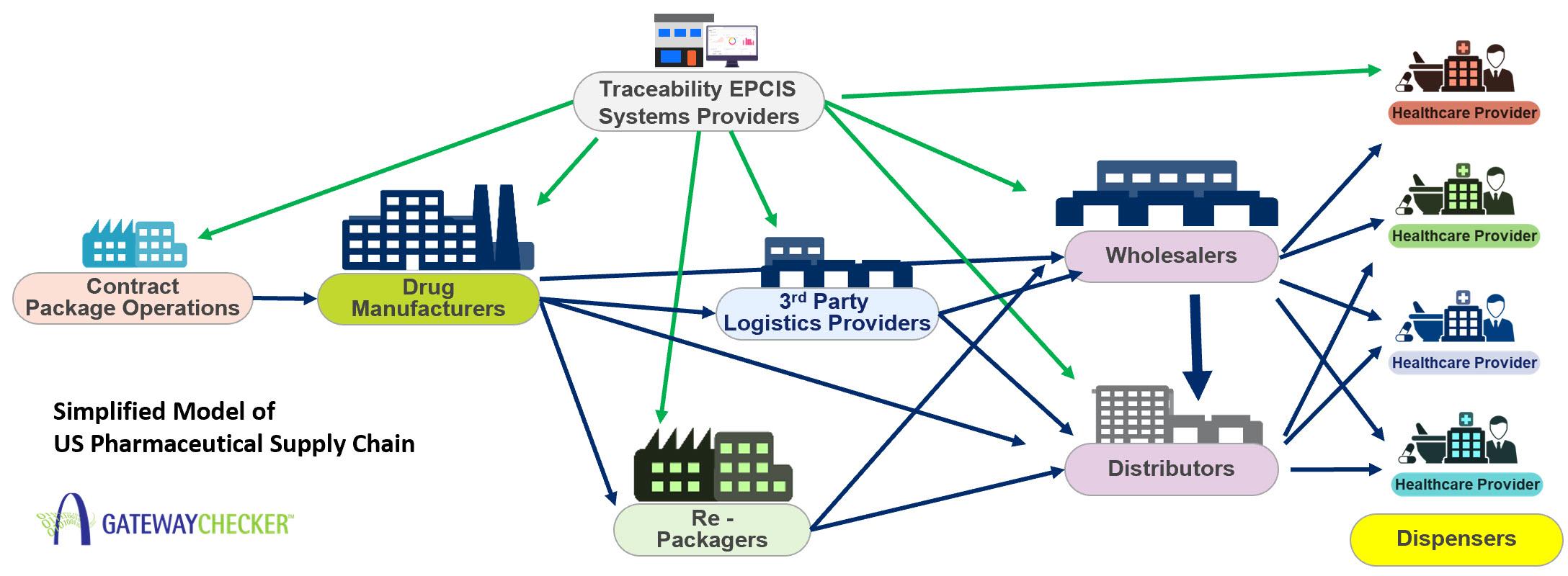
Every vial becomes a verifiable data point when unit-level serialization meets IoT oracles and a permissioned ledger. As drugs move from fill-finish to wholesaler, hospital pharmacy, and ultimately the bedside, signed telemetry and scan events are streamed through gateways that attest to who handled the product, where it traveled, and under what conditions. Smart contracts enforce chain-of-custody and temperature SLAs, while private channels preserve sensitive commercial data. The result is a tamper-evident audit trail that unifies DSCSA/GS1 compliance with real-time operational insight-a system that blocks counterfeits, accelerates recalls, and supports bedside verification without exposing patient identities.
Hospitals can integrate the ledger’s attestations with existing EHR, WMS, and ERP workflows, transforming compliance checkpoints into proactive safety controls. Deviations trigger automated playbooks-quarantines, notifications, and replenishment requests-backed by cryptographic proofs. Pharmacy leaders gain transparency across procurement, compounding, and administration, while manufacturers and distributors share a synchronized truth through role-based access. Below are core building blocks and an example of how event attestations drive measurable actions from dock to dose.
- Serialization: GS1 2D/Datamatrix or RFID at unit and case levels, linked to batch and expiry.
- IoT Oracles: Gateways sign temperature, shock, and location readings to prevent spoofing.
- Permissioned Ledger: Fabric/Quorum networks with private data collections for selective disclosure.
- Smart Contracts: Automated checks for excursions, diversion, and out-of-sequence scans.
- Interoperability: FHIR, EPCIS 2.0, and REST hooks into EHR, WMS, and recall systems.
- Analytics: Real-time anomaly scoring and geofencing for routes and care sites.
| Event | On‑chain Proof | Automated Action |
|---|---|---|
| Manufacture | Batch + serial hash | Release to distribution |
| Cold‑chain transit | Signed temp stream | Auto‑quarantine on excursion |
| Receiving | Custody attestation | Stock entry + lot match |
| Dispensing | Unit scan lineage | Pick verify + recall check |
| Bedside scan | Final authenticity proof | EHR document + block admin on fail |
Clinical trial integrity and evidence provenance through time stamped protocol locks and zero knowledge audits
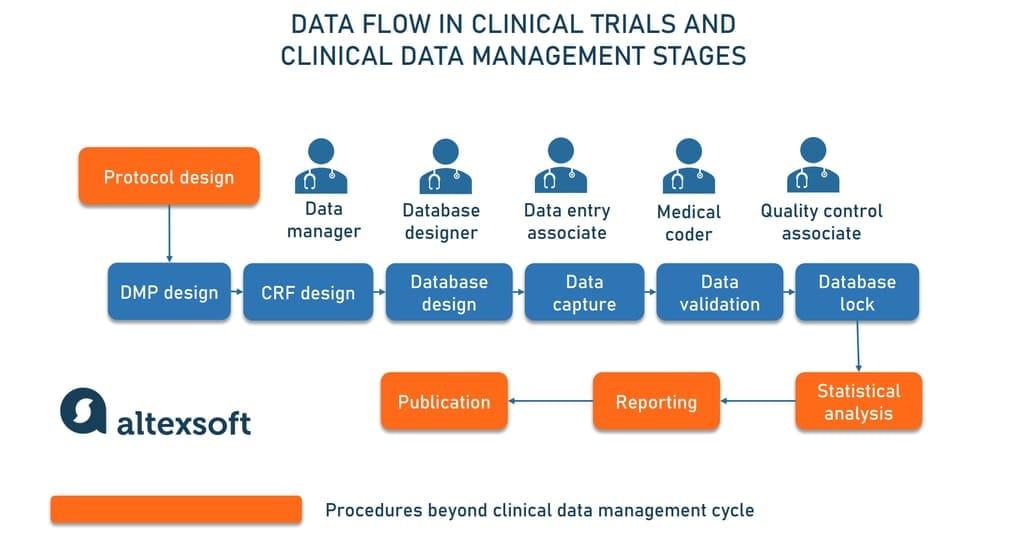
Locking trial blueprints before first enrollment creates a tamper-evident baseline: the protocol, statistical analysis plan, randomization algorithm, and amendment policy are hashed, time-stamped, and anchored to a ledger. Every subsequent change is versioned with a new hash, linked to the prior state, and accompanied by a zero-knowledge proof that the modification adheres to pre-declared governance. Auditors can verify adherence to endpoints, sample sizes, and exclusion criteria without accessing raw patient data-proving integrity while preserving privacy and blinding.
- Precommitment: Detects endpoint-switching and p-hacking via immutable, time-stamped anchors.
- Selective reporting control: ZK proofs attest all predefined outcomes were analyzed.
- Blinding integrity: Prove randomization fairness without revealing arms or seeds.
- Amendment traceability: Each change is cryptographically linked to rationale and approvals.
- Cross-site coherence: Multi-center trials share one source of truth without exposing PHI.
- Regulatory confidence: Readable attestations; raw data stays in secure enclaves.
A provenance-first pipeline binds every artifact-consent templates, eCRF schemas, device firmware checksums, data transformations-to an on-chain anchor and a verifiable chain-of-custody. Investigators retain control of sensitive content off-chain; regulators and sponsors receive portable proofs of correctness (e.g., “analysis followed SAP v1.3”) instead of spreadsheets of PHI. Interoperability with FHIR resources and audit logs lets sites plug in existing EDC systems while gaining cryptographic assurances. The result is evidence that is reproducible by design, with trust enforced by math rather than memos.
| Artifact | On-chain Anchor | Visibility | ZK Proof |
|---|---|---|---|
| Protocol & SAP | Hash + timestamp | Public | Unchanged endpoints |
| Randomization | Commitment | Hidden | Fair draw |
| Data transform | Code digest | Public | Pipeline fidelity |
| Adverse events | Merkle root | Permissioned | Complete reporting |
| Amendments | Version link | Public | Policy compliance |
Smarter claims processing and prior authorization via rules aware smart contracts and transparent dispute resolution
Imagine clinical policies expressed as machine-readable rules that evaluate each claim the moment it’s submitted. Rules-aware contracts check eligibility, coverage tiers, and documentation references, then post a time-stamped decision trail visible to authorized parties. Pre-approval can be issued as a tokenized authorization linked to the procedure, provider, and timeframe, with expirations and conditions encoded upfront. Sensitive documents stay off-chain, while hash-linked proofs and consented access keep workflows compliant and auditable without paper chases.
- Instant pre-checks: formulary, medical-necessity, and duplicate-detection validations.
- Evidence-linked decisions: each rule cites the guideline it relied on.
- Privacy by design: off-chain records, on-chain fingerprints and permissions.
- Adaptive rules: policy updates propagate via versioned contracts and oracles.
| Stakeholder | Smart Rule | Outcome |
|---|---|---|
| Provider | Medical-necessity logic | Fewer denials |
| Payer | Coverage-limit checks | Lower leakage |
| Patient | Real-time co-pay math | No surprises |
| Auditor | Immutable trails | Faster reviews |
When disagreements arise, the ledger becomes a transparent dispute ledger, recording evidence submissions, timers, and outcomes. Funds can be placed in escrow with programmable milestones, releasing partial payments when uncontested services clear while contested items proceed to tiered review. Time-boxed stalemates auto-escalate to neutral arbitration modules, and final rulings settle instantly with fee splits and rationale attached to the case file. The result is fewer bottlenecks, clearer incentives, and verifiable fairness from first review to final settlement.
- Escrow + milestones: pay what’s clear, isolate the rest.
- Appeal tiers: coded deadlines, evidence gates, and SLAs.
- Arbitration pools: independent reviewers matched on specialty.
- KPIs on-chain: denial rates, cycle times, and win/loss insights.
The Way Forward
At the bedside, the most effective technologies are the ones that don’t ask for applause. If blockchains find a role here, it will be because their specific strengths-shared provenance, tamper-evident records, programmable workflows-quietly support the work already in motion: safer supply chains, clearer consent, cleaner claims, traceable trials, and data-sharing that respects patient agency.
Getting there requires more engineering than evangelism. The questions are practical: Which problems truly need a distributed ledger? What belongs on-chain versus off-chain? How will keys, identities, and governance be managed when clinicians are busy and patients are vulnerable? How do we reconcile privacy with auditability, and standards with local workflows? The answers will come from careful pilots, transparent metrics, and a willingness to retire what doesn’t deliver value.
The near-term path is likely incremental and permissioned, anchored to narrow use cases with clear incentives and clear outcomes. Success will depend on interoperability with existing systems, fit-for-purpose regulation, credible threat modeling, and inclusive design that works for safety-net clinics as well as academic centers. Equity, usability, and energy costs are not footnotes; they are part of the clinical risk-benefit calculus.
If that discipline holds, the ledger will become another quiet instrument in the care orchestra-kept in tune by governance, nearly invisible in performance. Not a cure-all, not a headline, but a dependable rhythm section for trust. And in healthcare, trust is often the difference between technology that impresses and technology that heals.